HSR 在 Openwrt 22.03上的支持及验证
HSR 介绍
HSR (High-availability Seamless Redundancy)高可靠无缝冗余协议。所属的国际标准为IEC 62439,这是一个专注于解决高可靠自动化网络传输的标准。
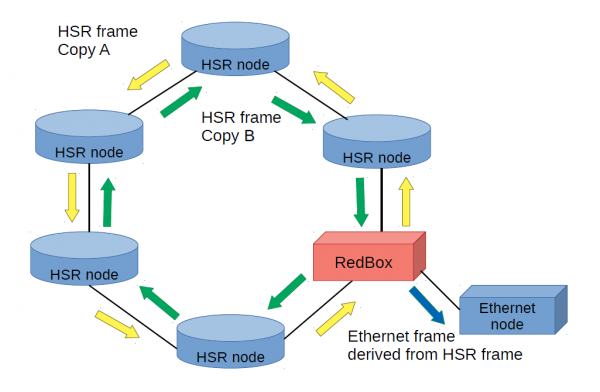
上图表示非HSR设备通过RedBox和HSR节点进行通信。HSR节点通信时,生成两个相同的数据包,一个数据包从一个端口顺时针发送,一个数据包从另一个端口逆时针发送。这样当某一个节点异常,即使顺时针方向的包不可达,逆时针方向的包也可以到达。
HSR 内核编译支持
Openwrt 22.03 使用的内核版本为:linux-5.10.111
开启HSR内核支持
xxxxxxxxxxmake kernel_menuconfig在 Networking support ---> Networking options ---> 下开启
xxxxxxxxxx< > High-availability Seamless Redundancy (HSR & PRP)开启后,配置会保存到
xxxxxxxxxxtarget/linux/x86/config-5.10添加调试工具
xxxxxxxxxxmake menuconfig默认openwrt中ip 命令使用的是busybox 集成的功能有限。需要支持专有的ip工具。
在 Network -> Routing and Redirection 下选中 ip-full
在 Network -> 下选中 iperf3 ,ethtool-full,tcpdump,fping
编译
make V=s
CONFIG_HSR 选项介绍
xxxxxxxxxxThis enables IEC 62439 defined High-availability Seamless Redundancy (HSR) and Parallel Redundancy Protocol (PRP).
If you say Y here, then your Linux box will be able to act as a DANH ("Doubly attached node implementing HSR") or DANP ("Doubly attached node implementing PRP"). For this to work, your Linux box needs (at least) two physical Ethernet interfaces.
For DANH, it must be connected as a node in a ring network together with other HSR capable nodes. All Ethernet frames sent over the HSR device will be sent in both directions on the ring (over both slave ports), giving a redundant, instant fail-over network. Each HSR node in the ring acts like a bridge for HSR frames, but filters frames that have been forwarded earlier.
For DANP, it must be connected as a node connecting to two separate networks over the two slave interfaces. Like HSR, Ethernet frames sent over the PRP device will be sent to both networks giving a redundant, instant fail-over network. Unlike HSR, PRP networks can have Singly Attached Nodes (SAN) such as PC, printer, bridges etc and will be able to communicate with DANP nodes.
This code is a "best effort" to comply with the HSR standard as described in IEC 62439-3:2010 (HSRv0) and IEC 62439-3:2012 (HSRv1), and PRP standard described in IEC 62439-4:2012 (PRP), but no compliancy tests have been made. Use iproute2 to select the protocol you would like to use.验证 HSR 支持生效
设备连线
将编译完毕的固件,烧录到两个相同的设备中。(每台设备应包含至少3个有线口)
设备A的 eth2 口连接到设备B的 eth3 口;
设备A的 eth3 口连接到设备B的 eth2 口。
配置hsr的接口
每台设备的eth2口和eth3口绑定到 hsr 接口上
x
ifconfig eth2 0.0.0.0 downifconfig eth3 0.0.0.0 downifconfig eth2 hw ether 38:7A:0E:1C:0E:80ifconfig eth3 hw ether 38:7A:0E:1C:0E:80ethtool -K eth2 hsr-rx-offload onethtool -K eth3 hsr-rx-offload onifconfig eth2 upifconfig eth3 upip link add name hsr0 type hsr slave1 eth2 slave2 eth3 supervision 45 version 1
配置设备A的hsr接口ip
xxxxxxxxxxifconfig hsr0 192.168.0.5配置设备B的hsr接口ip
xxxxxxxxxxifconfig hsr0 192.168.0.99
调试时可能需要删除hsr接口,命令如下
xxxxxxxxxxip link delete hsr0 type hsr连通性验证
设备A对设备B进行ping命令检测
xxxxxxxxxxroot@OpenWrt:/tmp# ping 192.168.0.99PING 192.168.0.99 (192.168.0.99): 56 data bytes64 bytes from 192.168.0.99: seq=0 ttl=64 time=1.112 ms64 bytes from 192.168.0.99: seq=1 ttl=64 time=1.053 ms^C--- 192.168.0.99 ping statistics ---2 packets transmitted, 2 packets received, 0% packet lossround-trip min/avg/max = 1.053/1.082/1.112 ms
在设备B上进行抓包分析
x
root@OpenWrt:/tmp# tcpdump -i eth2tcpdump: verbose output suppressed, use -v or -vv for full protocol decodelistening on eth2, link-type EN10MB (Ethernet), capture size 262144 bytes06:47:44.288950 38:7a:0e:1c:0e:80 (oui Unknown) > 70:ff:76:1c:0e:8c (oui Unknown), ethertype Unknown (0x892f), length 104: 0x0000: 105a fb4d 0800 4500 0054 5c95 4000 4001 .Z.M..E..T\.@.@. 0x0010: 5c5b c0a8 0005 c0a8 0063 0800 f2e6 16d9 \[.......c...... 0x0020: 0006 a2ee 4b4b 0000 0000 0000 0000 0000 ....KK.......... 0x0030: 0000 0000 0000 0000 0000 0000 0000 0000 ................ 0x0040: 0000 0000 0000 0000 0000 0000 0000 0000 ................ 0x0050: 0000 0000 0000 0000 0000 ..........
root@OpenWrt:/tmp# tcpdump -i eth3tcpdump: verbose output suppressed, use -v or -vv for full protocol decodelistening on eth3, link-type EN10MB (Ethernet), capture size 262144 bytes06:47:51.291890 38:7a:0e:1c:0e:80 (oui Unknown) > 70:ff:76:1c:0e:8c (oui Unknown), ethertype Unknown (0x892f), length 104: 0x0000: 005a fb58 0800 4500 0054 5e6d 4000 4001 .Z.X..E..T^m@.@. 0x0010: 5a83 c0a8 0005 c0a8 0063 0800 d303 16d9 Z........c...... 0x0020: 000d 57ca b64b 0000 0000 0000 0000 0000 ..W..K.......... 0x0030: 0000 0000 0000 0000 0000 0000 0000 0000 ................ 0x0040: 0000 0000 0000 0000 0000 0000 0000 0000 ................ 0x0050: 0000 0000 0000 0000 0000 ..........
root@OpenWrt:/tmp# tcpdump -i hsr0[173479.487875] device hsr0 entered promiscuous modetcpdump: verbose output suppressed, use -v or -vv for full protocol decodelistening on hsr0, link-type EN10MB (Ethernet), capture size 262144 bytes06:47:58.295238 IP 192.168.0.5 > 192.168.0.99: ICMP echo request, id 5849, seq 20, length 6406:47:58.295317 IP 192.168.0.99 > 192.168.0.5: ICMP echo reply, id 5849, seq 20, length 64
我们看到 eth2, eth3 上抓的icmp报文,ethertype 为0x892f 对应的正是HSR的协议。
xxxxxxxxxxHSR_EtherType = 0x892F在hsr0 接口上抓到的数据报文,已经是去掉了HSR填充的正常ICMP报文。
断连一根网线验证
HSR是两个接口都走数据,断掉其中一条通路,另一条通路依然可以达到。
将设备B上的eth3网线断开,依然抓包正常。
x
root@OpenWrt:/tmp# tcpdump -i eth3tcpdump: verbose output suppressed, use -v or -vv for full protocol decodelistening on eth3, link-type EN10MB (Ethernet), capture size 262144 bytes^C0 packets captured0 packets received by filter0 packets dropped by kernelroot@OpenWrt:/tmp# root@OpenWrt:/tmp# tcpdump -i eth2tcpdump: verbose output suppressed, use -v or -vv for full protocol decodelistening on eth2, link-type EN10MB (Ethernet), capture size 262144 bytes08:14:18.520356 38:7a:0e:1c:0e:80 (oui Unknown) > 01:15:4e:00:01:2d (oui Unknown), ethertype Unknown (0x892f), length 66: 0x0000: 1034 1a8c 88fb 0001 1a11 1706 34e7 0b1c .4..........4... 0x0010: 0e80 0000 0000 0000 0000 0000 0000 0000 ................ 0x0020: 0000 0000 0000 0000 0000 0000 0000 0000 ................ 0x0030: 0000 0000 ....
root@OpenWrt:/tmp# tcpdump -i hsr0[178664.303182] device hsr0 entered promiscuous modetcpdump: verbose output suppressed, use -v or -vv for full protocol decodelistening on hsr0, link-type EN10MB (Ethernet), capture size 262144 bytes08:14:23.573762 IP 192.168.0.5 > 192.168.0.99: ICMP echo request, id 5849, seq 5203, length 6408:14:23.573837 IP 192.168.0.99 > 192.168.0.5: ICMP echo reply, id 5849, seq 5203, length 64